HM Revenue and Customs are warning of the increased risk of phishing attacks at the time of the annual peak Self Assessment activity heading for the deadline of 31st January.
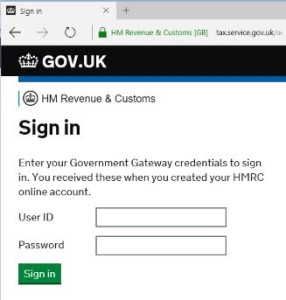
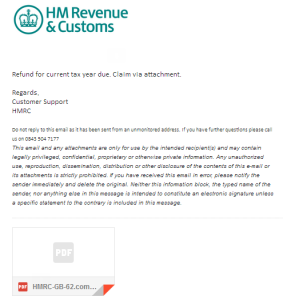
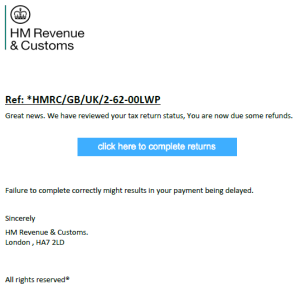
Typically, you will receive an email purporting to be from HMRC urging you to either request a payment of a tax refund, or to pay overdue tax or to avoid a penalty. A few years ago, these emails used to be easily recognisable with incorrect spelling and poor formatting. This has changed and most of these phishing emails look hard to tell apart from the genuine article. The telltale signs would be in the greeting of the email, which will be unlikely to contain your name (unless it is a spear phishing attempt) but rather will address you as “Dear taxpayer” or “Dear customer” or perhaps use your email address. You will either be invited to click on a link to go to a fake HMRC website and enter your bank or card details, or you will be urged to open a malicious attachment, usually a disguised application or a Microsoft Office file with an embedded malicious payload, or a crafted PDF file containing an exploit.
Please be careful, do not act in haste and do not rely on your Antivirus or Anti-malware protection to be 100% effective. You can find more information on HMRC phishing and how to report any attempts on https://www.gov.uk/topic/dealing-with-hmrc/phishing-scams.
To the left is an image of a phishing email I received today. As you can see, there is no personalisation, and the message is a bit abrupt with no reference numbers, dates etc. The attached PDF file did not actually contain any malware, rather it referred to a fake HMRC web page hosted on an australian website. The fake web page requested personal details, bank and card details and even a driving licence number and NI number, as well as mother’s maiden name. Perfect for identity theft and having your bank account cleaned out!
Of course, I took expert precautions and used special tools when investigating the email, the attachment and the website, to avoid any possible contamination. In this case, there was no malware present along the trail, this was a pure phishing attempt. However, the presence of malware must always be assumed and therefore I must urge any reader to avoid doing their own investigation and either delete any suspect emails immediately or forward them to an appopriate authority, such as phishing@hmrc.gsi.gov.uk.